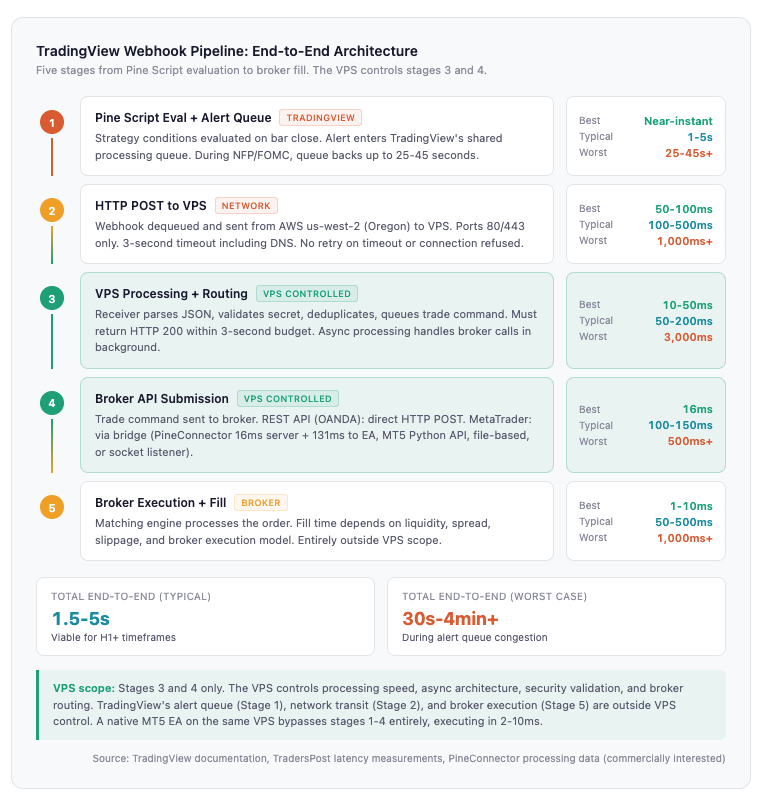
TradingView evaluates your Pine Script strategy on every bar close. Your broker fills the order when it receives one. Between those two events sits an HTTP POST request that needs a server listening on port 443, responding within 3 seconds, and running 24 hours a day, five days a week. That server is the VPS.
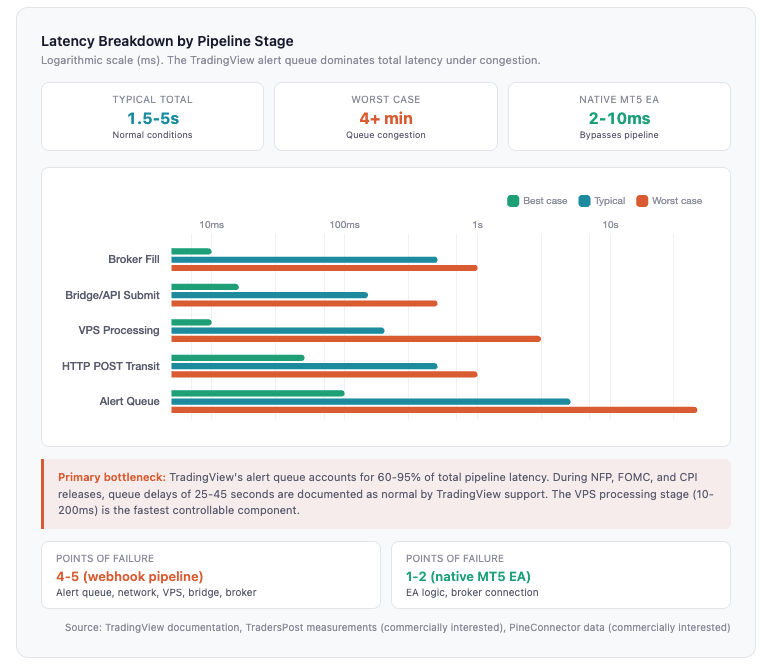
The webhook automation pipeline, from Pine Script signal to broker execution, typically completes in 1.5 to 5 seconds under normal conditions. During high-impact news events, TradingView’s internal alert queue can push that to 25 seconds or more. The architecture is viable for H1 and longer timeframes. It is not viable for scalping. Understanding where those seconds go, and which components you can actually control, determines whether this pipeline works for your trading or silently drops signals you never know about.
This guide covers the full execution chain: how TradingView sends webhooks, what a VPS-hosted receiver needs to parse and validate them, how to route signals to MetaTrader or REST API brokers like OANDA, and the layered security architecture required because TradingView does not sign its webhooks. Every latency figure and specification is sourced from TradingView’s official documentation, broker API references, developer forum measurements, or commercial provider data. Where a source has commercial interest, that interest is flagged explicitly.
The article is written for traders already using TradingView who want to automate execution through a VPS, and for traders weighing this pipeline against native MetaTrader EAs. If your strategy operates on M1 or M5 timeframes, the latency data in Section 2 will save you the setup time: native MT5 EAs executing in 2 to 10 milliseconds are the better architecture for those use cases.
How the Webhook Pipeline Works, End to End
A TradingView webhook trade passes through five stages before it becomes a filled order. Each stage adds latency, and each is a potential failure point. The VPS sits in the middle, controlling two of the five stages. The other three belong to TradingView’s infrastructure and the broker’s execution stack.
Stage 1: Pine Script evaluation and alert queue. When a bar closes and your strategy’s conditions are met, TradingView’s servers evaluate the Pine Script logic and place the resulting alert into an internal processing queue. Under normal conditions, this takes 1 to 5 seconds. The queue is the single largest variable in the pipeline. TradingView processes alerts sequentially, and when thousands of strategies trigger simultaneously (market opens, NFP, FOMC announcements), the queue backs up. Multiple independent sources, including TradingView’s own support responses, confirm that 25 to 45 seconds is considered a normal delay during congestion. A global outage on November 17, 2025 left alerts non-functional for an extended period. There is nothing the VPS can do about this stage.
Stage 2: HTTP POST to the VPS. Once TradingView dequeues the alert, it sends an HTTP POST request to the webhook URL you configured. The payload contains whatever you placed in the alert message field, either as application/json or text/plain. Network transit from TradingView’s servers in AWS us-west-2 (Oregon) to the VPS typically takes 100 to 500 milliseconds, depending on geographic distance. TradingView expects a 2xx response. If it receives HTTP 500 to 599, it retries up to 3 times at 5-second intervals. For any other failure (timeout, connection refused, 4xx error), the webhook is silently dropped with no retry and no queuing.
Stage 3: VPS processing and routing. The webhook receiver on the VPS parses the JSON payload, validates the authentication secret, checks for duplicate alerts, and routes the trade command to the appropriate broker API or MetaTrader bridge. A properly configured receiver (Flask behind Gunicorn, or FastAPI behind uvicorn, with nginx handling SSL termination) completes this in 10 to 50 milliseconds under typical conditions. The critical architectural requirement: the handler must return HTTP 200 to TradingView within the 3-second timeout window and process the actual trade asynchronously in the background. If broker API calls run synchronously and exceed 3 seconds, TradingView cancels the request and may retry, potentially causing duplicate execution.
Stage 4: Broker API order submission. The VPS sends the trade command to the broker’s execution infrastructure. For REST API brokers like OANDA, this is a straightforward HTTP POST to their order endpoint. For MetaTrader, this passes through a bridge layer (PineConnector’s cloud relay, the MT5 Python API, an EA-based socket listener, or a file-based handoff). Bridge processing adds 100 to 150 milliseconds for commercial solutions like PineConnector (16 milliseconds server-side, approximately 131 milliseconds to the EA).
Stage 5: Broker execution and fill. The broker’s matching engine processes the order. Fill time ranges from 1 to 10 milliseconds under ideal conditions to over 1 second during volatile markets. This stage is entirely broker-dependent. Liquidity, spread widening, slippage, and the broker’s own execution model all apply here, and none of them are within VPS scope.
The total pipeline under normal conditions: 1.5 to 5 seconds. Worst case during queue congestion and broker delays: 30 seconds to over 4 minutes.
For comparison, a native MT5 Expert Advisor running on the same VPS bypasses stages 1 through 4 entirely. The EA evaluates its logic locally on each tick and sends orders directly to the broker’s server. Typical latency: 2 to 10 milliseconds. Points of failure: 1 to 2, versus 4 to 5 for the webhook pipeline. This is not a criticism of the webhook approach. It is the architectural trade-off for using TradingView’s charting and Pine Script engine instead of MQL.
TradingView Webhook Specifications and Constraints
The webhook system has hard constraints that shape every architectural decision downstream. Understanding them before writing a single line of receiver code prevents the most common deployment failures.
Plan requirements and alert limits. Webhooks are not available on TradingView’s free Basic plan. The minimum is Essential at $12.95 per month (annual billing), which provides 20 active alerts with webhook access. Plus ($28.29/month) raises that to 100 alerts. Premium ($56.49/month) provides 400. Ultimate ($199.95/month) provides 1,000. The pricing difference matters less than a constraint most traders discover too late: alerts on Essential and Plus plans expire after approximately two months. They stop firing without any notification. No email, no log entry, no error. The alert simply goes silent. Premium and Ultimate plans offer open-ended alerts that never expire. For any production webhook pipeline running more than a handful of instruments, the silent expiry on lower-tier plans is a reliability risk that no amount of VPS engineering can detect or compensate for.
Two-factor authentication must be enabled on the TradingView account for webhooks to function. This is occasionally the reason a correctly configured pipeline produces no signals at all.
HTTP delivery mechanics. TradingView sends an HTTP POST request where the alert message body becomes the request payload. The Content-Type header is set automatically: application/json if the message is valid JSON, or text/plain if it is not. Only ports 80 and 443 are accepted. Any other port is rejected outright. IPv6 is not supported. The receiving server must have an IPv4 address.
The response timeout is 3 seconds, and that budget includes DNS resolution. If the VPS domain’s DNS is slow to resolve, or if the webhook receiver takes too long processing before returning a response, TradingView cancels the request. It does not retry on timeout. The signal is gone.
TradingView expects a 2xx HTTP response code. Any 3xx redirect is treated as a failure. Any 4xx client error is treated as a failure with no retry. For 5xx server errors (HTTP 500 through 599), TradingView retries up to 3 times at 5-second intervals, meaning a maximum of 4 total delivery attempts per trigger. This retry behavior is the only built-in redundancy in the entire pipeline. Outside the 5xx window, there is no queuing mechanism. A webhook that fails for any other reason is permanently lost.
Rate limiting. Strategy alerts are halted if they trigger more than 15 times within 3 minutes. No separate webhook-specific rate limit is documented beyond this threshold. For multi-instrument strategies that scan dozens of pairs on lower timeframes, this limit can throttle legitimate signals. The rate limit applies to the alert firing, not to webhook delivery, so even alerts that do not use webhooks count against the cap.
Published source IP addresses. TradingView officially documents four webhook source IPs, all hosted in AWS us-west-2 (Oregon):
52.89.214.238, 34.212.75.30, 54.218.53.128, 52.32.178.7
These are published specifically for firewall allowlisting. Restricting inbound connections on the VPS to these four addresses is the first layer of security against unauthorized webhook submissions. How to implement this on both Linux (UFW) and Windows Server is covered in Section 7.
HTTPS and SSL certificate verification. HTTPS is strongly recommended though not strictly required. When the webhook URL uses HTTPS, TradingView sends an SSL client certificate with the request. This certificate can be verified server-side to confirm that the request genuinely originated from TradingView, making it the strongest available authentication method for webhook receivers. Running the VPS webhook endpoint over plain HTTP works technically but eliminates this verification capability and transmits any payload secrets (including authentication tokens) in cleartext.
A domain name is practically necessary for HTTPS. Let’s Encrypt (Certbot) does not issue SSL certificates for bare IP addresses. A domain costs $1 to $10 per year. The Certbot setup on nginx (sudo certbot –nginx -d yourdomain.com) takes minutes, and certificates auto-renew on a 90-day cycle via systemd timer.
Structuring Webhook Payloads in Pine Script
The payload that arrives at the VPS is only as useful as the Pine Script that constructed it. A well-structured JSON message with explicit fields for action, symbol, quantity, and authentication simplifies every downstream decision the receiver needs to make. A loosely formatted string forces the receiver to guess, and guessing in trade execution is how duplicate orders and misrouted signals happen.
Three alert methods, three different constraint profiles. Pine Script provides three ways to generate alerts, and the choice determines how much control you have over the webhook payload.
The first is alertcondition(). It works only in indicators (studies), not strategies. The message parameter accepts a “const string,” meaning the value must be known at compile time. You cannot insert variables that change bar to bar. You can, however, use TradingView’s placeholder syntax ({{close}}, {{ticker}}, {{timenow}}) inside the message. TradingView replaces these at the moment the alert fires. The result is a static template with dynamic substitution, useful for simple signals but limited when the payload needs calculated values like ATR-based stop losses or position sizes.
The second is alert(). It works in both indicators and strategies and accepts a “series string,” meaning the message can include variables that change on every bar. This is the most flexible method. You can construct a complete JSON payload at runtime using str.tostring(), str.format(), and string concatenation, embedding calculated stop loss prices, dynamic lot sizes, indicator readings, and any other computed value. The alert() function also includes a freq parameter that controls firing frequency: alert.freq_once_per_bar (default), alert.freq_once_per_bar_close, and alert.freq_all.
The third is the strategy order fill alert. This is available only for strategies and triggers when the strategy’s broker emulator fills a simulated order. Only one alert per ticker is needed because it fires on every fill event. The key mechanism here is the alert_message parameter available in strategy.entry(), strategy.exit(), and strategy.order(). This parameter accepts a series string (fully dynamic), and its content is accessed in the alert message field via the placeholder {{strategy.order.alert_message}}. This lets each order carry its own custom payload while requiring only a single alert configuration.
“Once Per Bar Close” and why it matters for automation. On historical bars, Pine Script executes once per bar close. On realtime bars, it executes on each new tick. This creates a divergence between backtested behavior and live behavior if the alert frequency is set to “Once Per Bar” or “Every Tick,” because those settings can fire before the bar closes, potentially producing signals that would not appear in a backtest. “Once Per Bar Close” is the recommended setting for automated trading because it aligns live alert behavior with the backtest logic the strategy was validated against. For strategies, the calc_on_every_tick parameter enables mid-bar recalculation but increases repainting risk. Unless the strategy is specifically designed for intra-bar execution, leaving this disabled avoids a class of problems that are difficult to diagnose after deployment.
Building JSON payloads. Pine Script uses single quotes for string delimiters. JSON requires double quotes for keys and values. This is a frequent source of syntax errors for traders writing their first webhook payload. A strategy entry with a dynamic alert_message looks like this:
entryMsg = ‘{“action”:”buy”,”ticker”:”‘ + syminfo.ticker + ‘”,”qty”:’ + str.tostring(positionSize) + ‘,”sl”:’ + str.tostring(stopPrice) + ‘}’
strategy.entry(“Long”, strategy.long, alert_message=entryMsg)
In the alert configuration dialog, the Message field contains only: {{strategy.order.alert_message}}
TradingView replaces this placeholder with the full JSON string at the moment the order fills. The resulting HTTP POST to the VPS contains a parseable JSON body with the action, symbol, quantity, and stop loss price, all computed at runtime.
For simpler setups, a static template in the Message field with TradingView placeholders works without any Pine Script modification:
{“action”:”{{strategy.order.action}}”,”ticker”:”{{ticker}}”,”qty”:”{{strategy.order.contracts}}”,”price”:”{{close}}”,”position”:”{{strategy.market_position}}”,”time”:”{{timenow}}”}
All placeholders are case-sensitive and must be lowercase. {{strategy.order.action}} returns “buy” or “sell.” {{strategy.market_position}} returns “long,” “short,” or “flat.” {{strategy.position_size}} returns a signed value (positive for long, negative for short), while {{strategy.market_position_size}} returns the absolute value.
What the VPS receiver should expect. Regardless of construction method, the payload arriving at the VPS should contain at minimum: an authentication secret (for server-side validation), an action field with a constrained set of values, a ticker or symbol identifier, and a quantity. Including a magic number or strategy identifier helps the receiver route signals to the correct broker account when multiple strategies run simultaneously. Including {{timenow}} provides the alert fire timestamp for latency measurement and duplicate detection. The receiver’s job is validation and routing, not interpretation. The cleaner the payload leaves TradingView, the simpler every subsequent stage becomes.
VPS Receiver Architecture, from Flask to Systemd
The webhook receiver is a small application with a large responsibility. It accepts an HTTP POST, validates the payload, returns a 200 response before TradingView’s 3-second timeout expires, and queues the trade command for asynchronous execution against the broker API. The application itself is trivial. The production infrastructure around it, reverse proxy, SSL termination, process management, crash recovery, and async processing, is what separates a demo that works during testing from a pipeline that runs unattended for months.
Choosing a framework. Three options dominate community implementations. Python Flask is the most common in open-source TradingView webhook projects. It is simple, well-documented, and uses approximately 30 to 50 MB of RAM when running behind Gunicorn. Python FastAPI is the async-native alternative. It uses approximately 40 to 60 MB of RAM but handles concurrent webhook deliveries better than Flask because requests are processed asynchronously by default under uvicorn. Node.js Express is the third option, familiar to JavaScript developers and lightweight in memory. All three produce the same functional result: an HTTP endpoint that parses JSON and returns a response. The choice comes down to language familiarity and whether the broker integration library you need is available in Python or JavaScript.
Flask’s built-in development server is not production-grade. It handles one request at a time and has no crash recovery. In production, Flask runs behind Gunicorn with at least two worker processes (gunicorn -w 2 -b 127.0.0.1:5000 app:app). FastAPI runs behind uvicorn (uvicorn main:app –host 127.0.0.1 –port 8000). Both bind to localhost on an internal port. Neither should be exposed directly to the internet.
Why nginx sits in front. TradingView sends webhooks only to ports 80 and 443. The webhook application listens on an internal port (5000, 8000, 3000, or any other unprivileged port). nginx bridges the gap: it accepts incoming HTTPS traffic on port 443, terminates SSL, and proxies the request to the application on localhost. This is not optional architecture. Without a reverse proxy, the application would need to run as root to bind to port 443, handle SSL certificate management directly, and expose itself without any buffering or connection management layer.
The nginx configuration for this is straightforward. The server block listens on port 443 with SSL, references the Let’s Encrypt certificate and key files, and uses a location block to proxy_pass requests from the /webhook path to the internal application port. A second server block on port 80 returns a 301 redirect to HTTPS. The proxy_set_header directives for Host, X-Real-IP, X-Forwarded-For, and X-Forwarded-Proto are critical. Without X-Forwarded-For, the application sees 127.0.0.1 as the source IP for every request, which breaks IP-based allowlisting against TradingView’s published addresses.
SSL certificates. Let’s Encrypt provides free SSL certificates via Certbot. The setup is a single command (sudo certbot –nginx -d yourdomain.com), and Certbot modifies the nginx configuration automatically. Certificates expire every 90 days and auto-renew via a systemd timer that Certbot installs during setup. This requires a domain name. Let’s Encrypt does not issue certificates for bare IP addresses, so a domain ($1 to $10 per year) is a practical requirement for any production webhook receiver. Without HTTPS, TradingView still delivers webhooks, but the SSL client certificate that TradingView sends for origin verification is unavailable, and any authentication tokens in the payload travel in cleartext.
Process management and crash recovery. The webhook receiver must start automatically on boot and restart automatically on crash. On Linux, a systemd unit file handles both. The key directives are Restart=always and RestartSec=5, which ensure the service restarts within 5 seconds of any unexpected exit. The unit file specifies the working directory, the Gunicorn or uvicorn command, and an EnvironmentFile directive pointing to the .env file where secrets (webhook authentication tokens, broker API keys) are stored. After creating the unit file, systemctl enable registers it for automatic start on boot.
On Windows Server, NSSM (Non-Sucking Service Manager) provides equivalent functionality. It wraps the Python or Node.js process as a Windows service, handles crash restarts automatically, and runs the service even when no user is logged in via RDP. For Node.js specifically, PM2 offers process management with built-in log rotation and cluster mode (pm2 start app.js –name webhook && pm2 save && pm2 startup).
The practical difference between a systemd-managed service and a manually started script in a terminal session: when the VPS reboots after a kernel update at 3am on a Sunday, the systemd service is back online in seconds. The terminal script is not running, and every webhook that fires until someone notices and logs in to restart it is permanently lost.
The async processing pattern. This is the architectural decision that prevents the most common production failure. TradingView’s 3-second timeout means the webhook handler cannot make broker API calls synchronously within the request lifecycle. A market order to OANDA’s API might return in 200 milliseconds, or it might take 2 seconds during volatile conditions. An MT5 Python API call through a local bridge might normally complete in 100 milliseconds but stall during a MetaTrader reconnection event. If any of these exceed the 3-second budget, TradingView cancels the request, receives no response, and may retry, which risks duplicate execution.
The solution is to separate acknowledgment from execution. The webhook handler receives the POST, validates the payload structure and authentication secret, writes the trade command to a queue (Redis, SQLite, or even an in-memory queue for simpler setups), and returns HTTP 200 immediately. A separate worker process reads from the queue and executes broker API calls at its own pace. If the broker API is temporarily unavailable, the command stays in the queue and retries rather than being lost.
This pattern also provides a natural deduplication checkpoint. TradingView can send up to 4 copies of the same alert (1 original plus 3 retries on 5xx errors). The queue consumer checks whether a trade command with the same strategy name, ticker, timestamp, and action has already been processed within a configurable time window. If it has, the duplicate is logged and discarded.
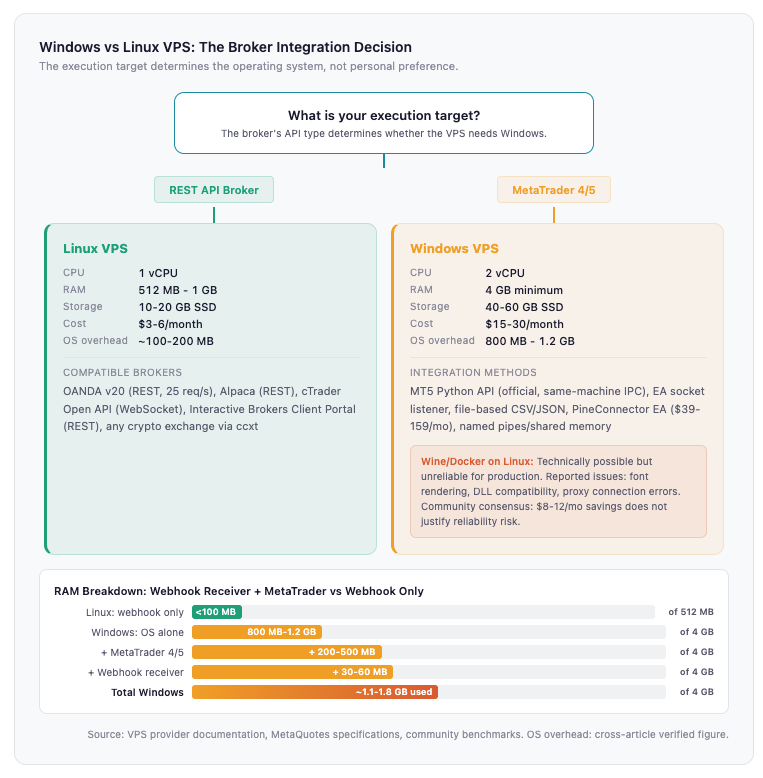
VPS sizing for webhook-only receivers. The resource footprint is minimal. Flask or FastAPI behind a reverse proxy with nginx collectively uses under 100 MB of RAM. A 1 vCPU, 512 MB to 1 GB RAM Linux VPS at $3 to $6 per month (DigitalOcean, Vultr, Hetzner) handles this workload comfortably with headroom for logging, monitoring, and the queue backend. If MetaTrader also runs on the same VPS, the requirements change significantly: 2 vCPU, 4 GB RAM minimum on a Windows VPS at $15 to $30 per month, because MetaTrader 4 or 5 alone uses 200 to 500 MB of RAM and Windows Server’s OS overhead consumes 800 MB to 1.2 GB before any application starts.
Routing Webhooks to Brokers
The webhook has arrived at the VPS, passed validation, and entered the processing queue. The next decision is where it goes. The broker integration method determines whether the VPS runs Linux or Windows, whether a third-party bridge is involved, and whether the monthly infrastructure cost is $5 or $60.
REST API brokers: direct integration from the webhook receiver. If the broker offers a REST API, the VPS can route trade commands directly without any bridge software, MetaTrader installation, or additional service layer. The webhook receiver’s queue worker makes an HTTP request to the broker’s order endpoint, authenticated with an API key stored in the VPS environment variables. No intermediary. No additional point of failure.
OANDA’s v20 API is the most webhook-friendly option for forex. Orders are submitted via POST to /v3/accounts/{accountID}/orders with Bearer token authentication. The Python wrapper (oandapyV20) simplifies the integration, though direct HTTP requests work equally well. Rate limit is 25 requests per second, which is generous for webhook-driven trading. The API is well-documented, the demo environment mirrors production, and the entire setup runs on a Linux VPS with no Windows dependency.
Alpaca provides a similarly clean REST API focused on US stocks. Interactive Brokers offers more asset coverage but uses a socket-based client-server architecture that requires TWS or IB Gateway running locally, which means a persistent socket connection, a maximum of 50 messages per second, and significantly more architectural complexity than a stateless REST call. cTrader’s Open API uses WebSocket with Protobuf (or JSON) and OAuth2 authentication. Official SDKs exist for C#, Java, Python, and JavaScript. The learning curve is steeper than REST but the performance is higher.
For traders whose broker exposes a REST API, the infrastructure equation is simple: a Linux VPS at $3 to $6 per month running the webhook receiver and making direct API calls. No Windows license, no MetaTrader, no bridge subscription.
MetaTrader integration: bridging the gap. MT4 and MT5 have no native webhook receiver. They do not expose a REST API. They are desktop applications designed around a GUI, an event-driven scripting language (MQL4/MQL5), and a proprietary connection to the broker’s trade server. Getting a webhook payload from the VPS into a MetaTrader order requires a bridge, and five methods exist with meaningfully different trade-offs.
The MT5 Python API is the official MetaQuotes library (pip install MetaTrader5). It connects Python to a running MT5 terminal via interprocess communication and exposes functions including mt5.order_send() with parameters for action, symbol, volume, type, price, stop loss, take profit, and deviation. The constraint is hard: both Python and MT5 must run on the same Windows machine. The library is Windows-only. This means the webhook receiver and MetaTrader must share a VPS, which pushes the minimum spec to 2 vCPU, 4 GB RAM on a Windows VPS at $15 to $30 per month.
EA-based socket listeners take a different approach. An Expert Advisor running inside MetaTrader opens a TCP connection or uses WebRequest() to poll a local HTTP endpoint for commands. The webhook receiver exposes a localhost API that the EA checks periodically. When a command is waiting, the EA executes it through MetaTrader’s native order functions. This decouples the webhook receiver from the MT5 Python API dependency but adds polling latency.
File-based communication is the simplest method. The webhook receiver writes trade commands to a CSV or JSON file in a shared directory. An EA periodically reads the file and executes any pending trades. No DLL imports needed. Works on both MT4 and MT5. The trade-off is latency: the polling interval (typically 100 to 500 milliseconds) adds delay on top of the pipeline’s existing 1.5 to 5 seconds. For H1+ strategies where seconds are not material, this is acceptable. For anything faster, it is not.
Named pipes and shared memory offer lower latency than file-based communication but require DLL imports in MQL, which some brokers restrict. Tools like PyTrader use socket-based IPC between Python and MT4/MT5 and provide a drag-and-drop EA that handles the MetaTrader side.
Commercial bridge services. For traders who want webhook-to-MetaTrader execution without building the bridge themselves, commercial services handle the middleware.
PineConnector is the dominant solution for MT4/MT5. The architecture routes TradingView alerts through PineConnector’s cloud infrastructure (hosted on Azure), where the signal is processed and forwarded to a PineConnector EA running on the trader’s MetaTrader terminal. The EA polls and receives commands. Reported processing: 16 milliseconds server-side, approximately 131 milliseconds to the EA, roughly 100 milliseconds for EA execution. Pricing runs from $39 per month (1 account) to $159 per month (10 accounts), with a 14-day free trial. PineConnector uses comma-separated plain text rather than JSON. The format is LicenseID,Command,Symbol,Parameters. One significant limitation: orders including stop loss and take profit cannot be modified after placement, and no data feeds back from MetaTrader to TradingView. PineConnector claims over 66,000 traders and 167 million signals processed. These figures come from the provider and have not been independently verified.
TradingConnector ($14.99 per month) takes a serverless approach. A Chrome extension intercepts TradingView alerts in-browser and forwards them locally to an EA via a local executable. Sub-second latency, no cloud dependency. The constraint: Chrome must stay open on the same machine as MetaTrader at all times. A VPS eliminates the home PC uptime problem but the Chrome requirement adds a failure point that purpose-built webhook receivers do not have.
TradersPost ($250 per month for unlimited) is JSON-based with sophisticated order types including limit, stop, stop-limit, trailing stop, and risk-based sizing. Its focus is US stocks, options, futures, and crypto rather than forex. Authentication uses a UUID and password embedded in the webhook URL.
WebhookTrade offers a fully cloud-based MT4/MT5 bridge that requires no VPS, no EA installation, and works with email alerts in addition to webhooks. The trade-off is credential security: the service connects to MetaTrader via broker credentials that you provide to their platform.
The credential security question. Every commercial bridge that routes through a cloud intermediary requires either broker API credentials or MetaTrader account access to be shared with the service provider. A self-hosted receiver on the trader’s own VPS keeps credentials local. For traders running significant capital, this distinction matters. For traders who prioritize setup speed over credential control, commercial bridges reduce deployment time from hours or days to 10 to 30 minutes.
Security Architecture for Webhook Receivers
TradingView does not sign its webhooks. There is no HMAC header, no API key exchange, no OAuth flow. The webhook URL is the only credential. Anyone who discovers it, through a misconfigured log, a shared screenshot, a compromised bridge service, or brute-force scanning, can send trade commands that the receiver will execute unless the VPS is configured to reject them. Security for this pipeline is not a feature you enable. It is a stack of independent layers, each implemented on the VPS, each catching what the previous one missed.
Layer 1: Firewall IP restriction. TradingView publishes four source IP addresses for webhook delivery, all in AWS us-west-2. The VPS firewall should restrict inbound traffic on ports 80 and 443 to these four addresses plus whatever IP is used for SSH administration. On Linux with UFW:
sudo ufw default deny incoming sudo ufw allow from 52.89.214.238 to any port 443 sudo ufw allow from 34.212.75.30 to any port 443 sudo ufw allow from 54.218.53.128 to any port 443 sudo ufw allow from 52.32.178.7 to any port 443 sudo ufw allow 22/tcp sudo ufw enable
On Windows Server, the equivalent is an inbound rule in Windows Defender Firewall with Advanced Security: allow TCP ports 80 and 443 with the Remote IP scope restricted to TradingView’s four addresses.
One implementation detail that trips up many deployments: when nginx is the reverse proxy, the application sees 127.0.0.1 as the source IP for every request because nginx is the one forwarding it. IP validation in the application code must check the X-Forwarded-For header, not request.remote_addr or the socket peer address. The nginx configuration must include proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for for this to work. Validating against the wrong header means either every request is rejected (if checking remote_addr against TradingView’s IPs) or every request is accepted (if skipping validation because remote_addr is always localhost). Both outcomes are silent.
Layer 2: Secret token validation. The webhook payload should include a shared secret that only the TradingView alert configuration and the VPS receiver know. In the TradingView alert message, this is a field in the JSON body:
{“secret”:”your_secret_token”,”action”:”buy”,”ticker”:”EURUSD”}
The receiver validates this field before processing anything else:
WEBHOOK_SECRET = os.environ.get(“WEBHOOK_SECRET”) if data.get(“secret”) != WEBHOOK_SECRET: return jsonify({“error”: “unauthorized”}), 403
The secret must be stored in an environment variable loaded from a .env file, never hardcoded in the application source. On Linux with systemd, the EnvironmentFile directive in the unit file points to the .env file. On Windows with NSSM, the AppEnvironmentExtra parameter sets environment variables for the service. TradingView explicitly warns against including broker API credentials in webhook message bodies. The authentication secret is a webhook-level token, separate from any broker credentials.
For deployments managing significant capital, dedicated secrets management services (AWS Secrets Manager, Azure Key Vault, HashiCorp Vault) provide rotation, access logging, and encrypted storage that a flat .env file does not.
Layer 3: TradingView SSL certificate verification. When the webhook URL uses HTTPS, TradingView sends an SSL client certificate with each request. This certificate can be verified server-side to confirm that the request originated from TradingView’s infrastructure. It is the strongest authentication mechanism available for this pipeline because it cannot be replicated by an attacker who merely knows the webhook URL and the shared secret. Implementing client certificate verification requires configuring nginx to request and validate the client certificate against TradingView’s certificate chain. This is more complex than the first two layers and not documented in most webhook tutorials, but for high-value accounts it closes the gap between “shared secret that could be leaked” and “cryptographic proof of origin.”
Layer 4: Input validation. Even with IP restriction, token validation, and certificate verification in place, the webhook payload itself should never be trusted blindly. The receiver should validate that the action field contains only expected values (buy, sell, close), the ticker matches a predefined list of allowed instruments, quantity and price fall within reasonable bounds (no 1,000-lot orders on an account sized for 0.1 lots), and string fields contain no injection payloads. This layer prevents a malformed or manipulated payload from reaching the broker API even if all outer layers pass. The validation logic is straightforward: a whitelist of acceptable values for each field, numeric range checks, and string sanitization.
Layer 5: Rate limiting. A final defensive layer prevents abuse even from authenticated sources. TradersPost uses 60 requests per minute and 500 per hour as benchmarks, which are reasonable starting points for a webhook receiver. Flask-Limiter and fastapi-limiter provide decorator-based rate limiting that requires minimal code. Rate limiting also serves as a safety net against runaway TradingView strategies that fire alerts faster than expected. A strategy that triggers 30 alerts in a minute due to a Pine Script logic error should be throttled at the receiver rather than allowed to submit 30 orders to the broker.
What these layers do not cover. All five layers protect the VPS receiver from unauthorized or malformed inbound requests. They do not protect against a compromised TradingView account (an attacker who gains access to the TradingView account can modify alert messages and webhook URLs), a compromised VPS (an attacker with shell access can read environment variables and broker API keys), or a compromised bridge service (commercial bridges that store broker credentials are an additional attack surface). The scope of security engineering on the VPS is limited to the VPS. Account-level security (strong passwords, two-factor authentication on TradingView and broker accounts, SSH key-only authentication on the VPS) is the trader’s responsibility and sits outside this article’s infrastructure scope.

Failure Modes and What the VPS Cannot Fix
The webhook pipeline has 4 to 5 independent failure points. The VPS controls one of them. Pretending otherwise would make this article less useful and less honest than the reader deserves. A trader deploying this architecture should know exactly where signals can be lost, which failures are recoverable, and which ones result in a trade that never executes with no indication that anything went wrong.
TradingView alert queue congestion. The alert queue is the single largest source of delay and the one the trader has no control over. TradingView processes alerts through a shared queue, and when thousands of strategies fire simultaneously during market opens or high-impact news releases (NFP, FOMC, CPI), the queue backs up. Multiple independent sources, including TradingView’s own support responses, describe 25 to 45 seconds as a normal delay during these events. TradersPost measured typical delivery at approximately 1 to 1.5 seconds using the {{timenow}} parameter comparison method, with occasional spikes up to 30 seconds. A global outage on November 17, 2025 left alerts non-functional for an extended period. The VPS was online. The receiver was running. No signals arrived.
An additional measurement caveat: TradingView’s alert log timestamps may be backdated to when the condition was met, not when the webhook was actually sent. The only reliable way to measure true delivery latency is comparing TradingView’s {{timenow}} value against the VPS server’s receipt timestamp. Traders who see “instant” delivery in TradingView’s alert log may be looking at the wrong timestamp.
Silent alert expiry. Alerts on Essential and Plus plans expire after approximately two months. They do not send a notification when they stop. They do not log an expiry event. The alert simply ceases to fire. A trader who set up the pipeline two months ago and assumed it was running may have been unmonitored for days or weeks before noticing the silence. The VPS cannot detect this because from the VPS perspective, no webhook arrives, which is indistinguishable from a period where the strategy’s conditions were never met. Premium and Ultimate plans eliminate this failure mode entirely. For any production deployment, the cost difference between Essential ($12.95/month) and Premium ($56.49/month) is insurance against a failure mode that is both silent and undetectable from the infrastructure side.
No catch-up mechanism. If the VPS is offline when TradingView fires an alert, whether due to a reboot, a crash, a network outage, or a provider maintenance window, the signal is permanently lost. TradingView’s retry mechanism covers only HTTP 500 to 599 responses (3 retries at 5-second intervals). A connection refused response, a timeout, or a DNS resolution failure receives no retry and no queuing. The alert fires in TradingView’s log. The webhook goes nowhere. There is no “pending delivery” state. There is no catch-up when the VPS comes back online.
This makes VPS uptime directly proportional to signal capture rate. A VPS with 99.99% uptime (52.6 minutes of downtime per year, or 4.38 minutes per month) reduces the window for missed signals to near zero. A home PC with compounded availability of 90 to 97% (263 to 876 hours of downtime per year) leaves significant gaps. The difference between a dedicated VPS and a home computer is not performance. It is the probability that the server is listening when the signal arrives.
Duplicate execution. TradingView can send up to 4 copies of the same alert: the original delivery plus 3 retries if the VPS returns HTTP 500 to 599. If the receiver processes the trade on the first delivery but returns a 500 error due to a downstream failure (broker API timeout, unhandled exception after order submission), TradingView retries. Without deduplication logic, the same trade executes up to four times. The queue-based architecture described in Section 5 provides the natural checkpoint: each incoming webhook is assigned a composite identifier (strategy name, ticker, timestamp, action), and the queue consumer checks whether that identifier was already processed within a configurable time window. Duplicates are logged and discarded. Without this check, the retry mechanism that is supposed to improve reliability becomes a source of unintended position accumulation.
Broker API downtime. The webhook arrives at the VPS, passes validation, and enters the processing queue. The queue worker attempts to submit the order to the broker API. The broker’s API is down, returning connection errors or HTTP 503. If the receiver processes synchronously, the order fails and is lost. The queue-based architecture retries against the broker with configurable backoff, which covers brief outages (seconds to minutes). Extended broker downtime (the API is offline for an hour during a platform migration) means the trade signal is stale by the time the broker is available. For H1+ strategies, a 10-minute broker outage during a quiet session may not matter. For a signal triggered during a volatility spike, the entry price has moved by the time the order can be placed. The queue provides durability. It does not provide relevance. A trade command that is 30 minutes old may be worse than no trade at all.
High-volatility event risk. Multiple sources recommend pausing webhook automation 5 or more minutes before and after high-impact economic releases. Alert queue congestion, broker spread widening, liquidity thinning, and the combination of all three create conditions where the pipeline’s typical 1.5 to 5 second latency can stretch to 30 seconds or more, and the fill price may bear little resemblance to the signal price. Approximately 25% of TradingView users report alert glitches during volatility spikes according to Downdetector data, though this figure comes from a commercial platform’s blog post and should be treated as directional rather than precise. The practical guidance: if the strategy does not specifically target news events, disabling webhook alerts around scheduled high-impact releases removes the highest-risk window from the pipeline without affecting the rest of the trading week.
What a VPS does control. The VPS controls its own uptime, its response time to incoming webhooks, its security configuration, its async processing architecture, and its retry logic against broker APIs. A properly configured VPS with 99.99% uptime, sub-50ms processing, layered security, queue-based execution, and deduplication logic eliminates the VPS as a failure point. The remaining failure points, TradingView’s alert queue, TradingView’s platform availability, broker API availability, and market conditions, are outside VPS scope. Acknowledging this boundary honestly is more useful than implying that better infrastructure solves all of them.
FAQ
Can I use TradingView webhooks with a free plan?
No. Webhooks require a paid TradingView plan, starting at Essential ($12.95 per month with annual billing). The free Basic plan provides one active alert but no webhook capability. Essential provides 20 alerts with webhook access, Plus provides 100, Premium provides 400, and Ultimate provides 1,000. For production automation, note that Essential and Plus alerts expire silently after approximately two months, which makes Premium or Ultimate the safer choice for unattended pipelines.
Do I need a Windows VPS or a Linux VPS?
It depends entirely on the broker integration method. If the execution target is a REST API broker (OANDA, Alpaca, cTrader), a Linux VPS at $3 to $6 per month handles the webhook receiver with no Windows dependency. If the execution target is MetaTrader 4 or 5, a Windows VPS at $15 to $30 per month is required because MT4 and MT5 are native Windows applications and the official MT5 Python API is Windows-only. Running MT5 on Linux via Wine or Docker (gmag11/MetaTrader5-Docker) is technically possible but unreliable in production, with reported issues including font rendering failures, DLL compatibility problems, and proxy connection errors. Community consensus is that the $8 to $12 monthly savings from Linux does not justify the reliability risk for MetaTrader workloads.
How much RAM does the webhook receiver need?
Flask behind Gunicorn with nginx collectively uses under 100 MB of RAM. A 512 MB to 1 GB Linux VPS handles a webhook-only receiver comfortably with headroom for logging, the queue backend, and basic monitoring. If MetaTrader also runs on the same VPS, the minimum is 4 GB. MetaTrader 4 or 5 uses 200 to 500 MB depending on chart count and indicator load, and Windows Server’s OS overhead consumes 800 MB to 1.2 GB before any application starts. Sizing should account for the combined footprint, not just the receiver.
What happens if my VPS is offline when an alert fires?
The signal is permanently lost. TradingView retries only when the receiving server returns HTTP 500 through 599 (3 retries at 5-second intervals, maximum 4 total attempts). If the VPS is unreachable (connection refused, timeout, DNS failure), no retry occurs and no queuing mechanism holds the webhook for later delivery. The alert appears as fired in TradingView’s log, but the trade never executes. A VPS with 99.99% uptime reduces the window for missed signals to approximately 4.38 minutes per month. A home PC with typical compounded availability of 90 to 97% leaves 263 to 876 hours of downtime per year.
Is PineConnector worth the subscription versus building my own receiver?
PineConnector sets up in 10 to 30 minutes and handles the TradingView-to-MetaTrader middleware at $39 to $159 per month depending on account count. A self-hosted Flask receiver on a $5 to $6 per month Linux VPS takes hours to days to build and test but offers unlimited customization, local credential storage, and compatibility with any broker that has an API, not just MetaTrader. PineConnector also uses comma-separated plain text rather than JSON and cannot modify orders (stop loss, take profit) after placement. The trade-off is concrete: faster deployment and lower technical barrier versus lower ongoing cost, broader broker support, and full control over credential security. For traders running MT4 or MT5 who want to automate within a day, PineConnector is a reasonable starting point. For traders targeting REST API brokers, PineConnector is not applicable and a self-hosted receiver is the only option.
What timeframes work reliably with webhook automation?
H1 and above are well-suited. Typical end-to-end latency of 1.5 to 5 seconds is negligible relative to a 60-minute candle. H4 and daily timeframes are the ideal use case, where even worst-case delays of 30 seconds or more do not materially affect entry or exit quality. M15 is possible if the strategy can tolerate 30 to 60 seconds of execution delay without invalidating the signal logic. M5 is marginal because alert queue delays represent a significant portion of the candle duration. M1 is not suitable: delays of 25 to 45 seconds during queue congestion span entire candles, and the strategy would frequently be acting on stale signals. For anything below H1 where execution timing is critical, native MT5 Expert Advisors executing in 2 to 10 milliseconds on the same VPS are the architecturally superior choice.
References
- TradingView. Official webhook configuration documentation. Documents HTTP POST delivery mechanics, Content-Type auto-detection (application/json for valid JSON, text/plain otherwise), port restrictions (80 and 443 only), 3-second response timeout including DNS resolution, retry policy (3 retries at 5-second intervals for HTTP 500-599 only, no retries for timeouts or connection refusals), and the absence of any queuing mechanism for failed deliveries. Also publishes the four webhook source IP addresses (52.89.214.238, 34.212.75.30, 54.218.53.128, 52.32.178.7) in AWS us-west-2 for firewall allowlisting, and documents the SSL client certificate sent with HTTPS webhook requests for origin verification. Used throughout this article for all webhook delivery specifications, retry behavior, and security architecture. Source quality: primary platform documentation.
- TradingView. Plan comparison and pricing page. Documents current plan tiers (Basic, Essential, Plus, Premium, Ultimate), monthly pricing under annual billing ($0, $12.95, $28.29, $56.49, $199.95), active alert limits (1, 20, 100, 400, 1,000), webhook availability by tier (Essential and above), and alert expiry behavior (approximately 2 months on Essential/Plus, never on Premium/Ultimate). Also confirms two-factor authentication is required for webhook functionality. Pricing verified as of Q2 2026. Used in Sections 3 and 9 for plan requirements and the silent expiry failure mode analysis. Source quality: primary vendor documentation.
- TradingView. Pine Script v6 language reference. Documents the three alert generation methods: alertcondition() (indicators only, const string), alert() (indicators and strategies, series string with freq parameter options), and strategy order fill alerts with the alert_message parameter in strategy.entry()/strategy.exit()/strategy.order(). Confirms case sensitivity and lowercase requirement for all placeholder variables. Documents calc_on_every_tick behavior and the distinction between historical bar execution (once per close) and realtime bar execution (on each tick). Used in Section 4 for payload construction and alert frequency guidance. Source quality: primary platform documentation.
- TradingView. Placeholder variable reference. Documents standard alert placeholders ({{ticker}}, {{close}}, {{open}}, {{high}}, {{low}}, {{volume}}, {{time}}, {{timenow}}, {{interval}}) and strategy-specific placeholders ({{strategy.order.action}}, {{strategy.order.contracts}}, {{strategy.order.price}}, {{strategy.order.id}}, {{strategy.order.alert_message}}, {{strategy.market_position}}, {{strategy.position_size}}, {{strategy.market_position_size}}). Confirms {{strategy.order.action}} returns “buy” or “sell,” {{strategy.market_position}} returns “long,” “short,” or “flat,” and {{strategy.position_size}} is signed while {{strategy.market_position_size}} is absolute. Used in Section 4 for payload field specifications. Source quality: primary platform documentation.
- TradingView. Alert log and webhook status interface. Provides a “Webhook status” column in the alert management panel for monitoring delivery success and failure. Multiple TradingView support responses confirm that 25 to 45 seconds of alert queue delay is considered normal during high-volume events. Used in Sections 2 and 8 for latency analysis and the alert queue congestion failure mode. Source quality: primary platform support responses, though delay figures reflect general guidance rather than documented SLAs.
- TradingView. November 17, 2025 service disruption. A global outage left alerts non-functional for an extended period. Referenced in multiple community reports. Used in Section 8 as evidence that platform-level failures are outside VPS control. Source quality: user-reported incident, consistent across multiple independent reports.
- TradersPost. Webhook delivery latency measurements. Measured typical webhook delivery at approximately 1 to 1.5 seconds using the {{timenow}} parameter comparison method, with occasional spikes up to 30 seconds. TradersPost founder Mike Christensen states his trades last “15 minutes or longer” and finds the latency manageable. TradersPost documentation also references rate limiting benchmarks of 60 requests per minute and 500 per hour as reasonable thresholds for webhook receivers. Used in Sections 2 and 8 for latency data and in Section 7 for rate limiting benchmarks. Source quality: commercially interested (TradersPost is a paid webhook bridge service at $250/month), but latency measurement methodology is documented and findings are directionally consistent with other independent reports.
- MetaQuotes. MT5 Python API documentation (PyPI: MetaTrader5). Documents the official Python integration library for MetaTrader 5, including mt5.order_send() with parameters for action, symbol, volume, type, price, stop loss, take profit, and deviation. Confirms the library is Windows-only and requires both Python and the MT5 terminal running on the same machine via interprocess communication. Used in Section 6 for the MetaTrader integration architecture. Source quality: primary platform documentation.
- OANDA. v20 REST API reference. Documents the order submission endpoint (POST /v3/accounts/{accountID}/orders), Bearer token authentication, demo and live base URLs (api-fxpractice.oanda.com, api-fxtrade.oanda.com), and 25 requests per second rate limit. Python wrapper: oandapyV20. Used in Section 6 as the primary example of a webhook-friendly REST API broker. Source quality: primary broker documentation.
- Interactive Brokers. TWS API documentation. Documents the socket-based client-server architecture requiring TWS or IB Gateway running locally, Python ibapi package with EClient/EWrapper pattern, and 50 messages per second rate limit. Used in Section 6 for the multi-asset broker integration comparison. Source quality: primary broker documentation.
- cTrader. Open API documentation. Documents WebSocket/Protobuf (or JSON) protocol, OAuth2 authentication, and official SDKs for C#, Java, Python, and JavaScript. Used in Section 6 for the broker integration comparison. Source quality: primary platform documentation.
- PineConnector. Product documentation and syntax reference. Documents the architecture (TradingView alert to PineConnector cloud on Azure to PineConnector EA on MT4/MT5), comma-separated plain text format (LicenseID,Command,Symbol,Parameters), processing times (16ms server-side, approximately 131ms to EA, roughly 100ms EA execution), pricing ($39 to $159 per month, 14-day free trial), and the limitation that orders cannot be modified after placement. Claims 66,000+ traders and 167M+ signals processed. Operated by Nautilion Pte Ltd (Singapore). Used in Section 6 for the commercial bridge analysis. Source quality: commercially interested. User count and signal volume claims are provider-sourced and have not been independently verified. Processing time figures are provider-measured.
- TradingConnector. Product documentation. Documents the serverless architecture (Chrome extension plus local executable plus EA, all on same PC), sub-second latency, $14.99 per month pricing, and the requirement that Chrome must remain open. Used in Section 6 as a commercial bridge alternative. Source quality: commercially interested.
- WebhookTrade. Product documentation. Documents the fully cloud-based MT4/MT5 bridge requiring no VPS or EA installation, broker credential-based connection, and email alert support enabling free TradingView plan usage. Used in Section 6 for the cloud-based bridge option and the credential security discussion. Source quality: commercially interested. Credential-sharing model noted as a security consideration.
- Community VPS deployment guides. DigitalOcean community tutorials, e-tinkers.com Flask deployment guide, and DevDungeon NSSM documentation provide implementation patterns for Flask/Gunicorn deployment on Linux, nginx reverse proxy configuration, systemd service management, and NSSM Windows service wrapping. Used in Section 5 for receiver deployment architecture. Source quality: community documentation, generally reliable for configuration patterns.
- Let’s Encrypt / Electronic Frontier Foundation. Certbot documentation. Documents free SSL certificate issuance, nginx integration (sudo certbot –nginx -d yourdomain.com), 90-day certificate expiry, and automatic renewal via systemd timer. Confirms certificates are not issued for bare IP addresses. Used in Sections 5 and 7 for SSL setup. Source quality: primary project documentation.
- Open-source GitHub repositories. fabston/TradingView-WebhookBot (approximately 1,500 stars, Python/Flask, forwards alerts to Telegram/Discord/Slack, no trading execution). robswc/tradingview-webhooks-bot (approximately 730 stars, Python/Flask, framework for custom trading logic). TheSnowGuru/PyTrader (Python plus MQL4/5, drag-and-drop EA connecting MetaTrader to Python via sockets). The dominant open-source pattern is Flask-based with a shared-secret “key” field for authentication. Used for architectural reference and to document the self-hosted alternative ecosystem. Source quality: open-source community projects with varying maintenance status.
- Downdetector / commercial platform blog. Reports approximately 25% of TradingView users experience alert glitches during volatility spikes. Used in Section 8 for the high-volatility event risk analysis. Source quality: the 25% figure originates from a commercial platform’s blog post citing Downdetector data. Treated as directional rather than precise, and flagged accordingly in the article text.
- VPS provider and community benchmark data. Flask plus Gunicorn plus nginx collectively under 100 MB RAM. Docker image for Flask webhook receiver: 45 MB (Alpine-based) to 147 MB (python:slim-based). Minimum VPS spec for webhook-only receiver: 1 vCPU, 512 MB to 1 GB RAM, $3 to $6 per month on Linux providers. Minimum for webhook plus MetaTrader: 2 vCPU, 4 GB RAM, $15 to $30 per month on Windows. Community consensus on MT5-on-Linux via Wine: unreliable for production, with font rendering failures, DLL compatibility issues, and proxy connection errors. Used in Sections 5, 6, and 9 for VPS sizing and the Windows vs Linux decision. Source quality: mixed. RAM figures are consistent across multiple community reports. Wine reliability assessment reflects community consensus across multiple forums (MQL5, ForexFactory, Reddit). Specific VPS pricing reflects publicly listed rates from providers (DigitalOcean, Vultr, Hetzner) as of Q2 2026.
Editorial Note
This article covers the infrastructure architecture for automating TradingView alerts through a VPS-hosted webhook receiver. It is not financial advice. The webhook pipeline is a signal routing mechanism. Whether the signals themselves produce profitable trades depends on the trading strategy, market conditions, broker execution quality, and liquidity, none of which are within the scope of VPS infrastructure or this article.
Latency figures throughout this article are reference ranges compiled from TradingView documentation, community measurements, and commercial provider data. Actual delivery times will vary based on TradingView’s internal queue load, VPS geographic location relative to both TradingView’s servers and the broker’s execution infrastructure, broker API performance, and network conditions at the time of execution. No latency figure in this article should be treated as a guarantee or SLA.
Pricing figures for TradingView plans, commercial bridge services, VPS providers, and domain registration reflect publicly documented rates as of Q2 2026 and may change. TradingView’s published webhook source IP addresses (used for firewall allowlisting) are current at the time of writing but could be updated by TradingView without notice. Traders relying on IP-based firewall rules should verify these addresses periodically against TradingView’s official documentation.
Several sources cited in this article have commercial interest in the data they publish. PineConnector, TradersPost, TradingConnector, and WebhookTrade are paid services whose documentation and performance claims are self-reported. The Downdetector-sourced figure on alert glitches during volatility (approximately 25% of users affected) originates from a commercial platform’s blog post and is treated as directional, not precise. VPS provider RAM and performance benchmarks come from providers with commercial interest in demonstrating their platforms’ capabilities. Where these sources are used, the commercial interest is noted in the article text and in the References section.
This article is published on a VPS provider’s website. The same evaluation criteria, technical analysis, and transparency standards apply to all architectures discussed, including scenarios where a VPS is not the optimal choice. For latency-sensitive strategies on M1 to M15 timeframes, the article explicitly recommends native MetaTrader Expert Advisors over the webhook pipeline, because that is the architecturally honest assessment regardless of the publisher’s commercial interest.